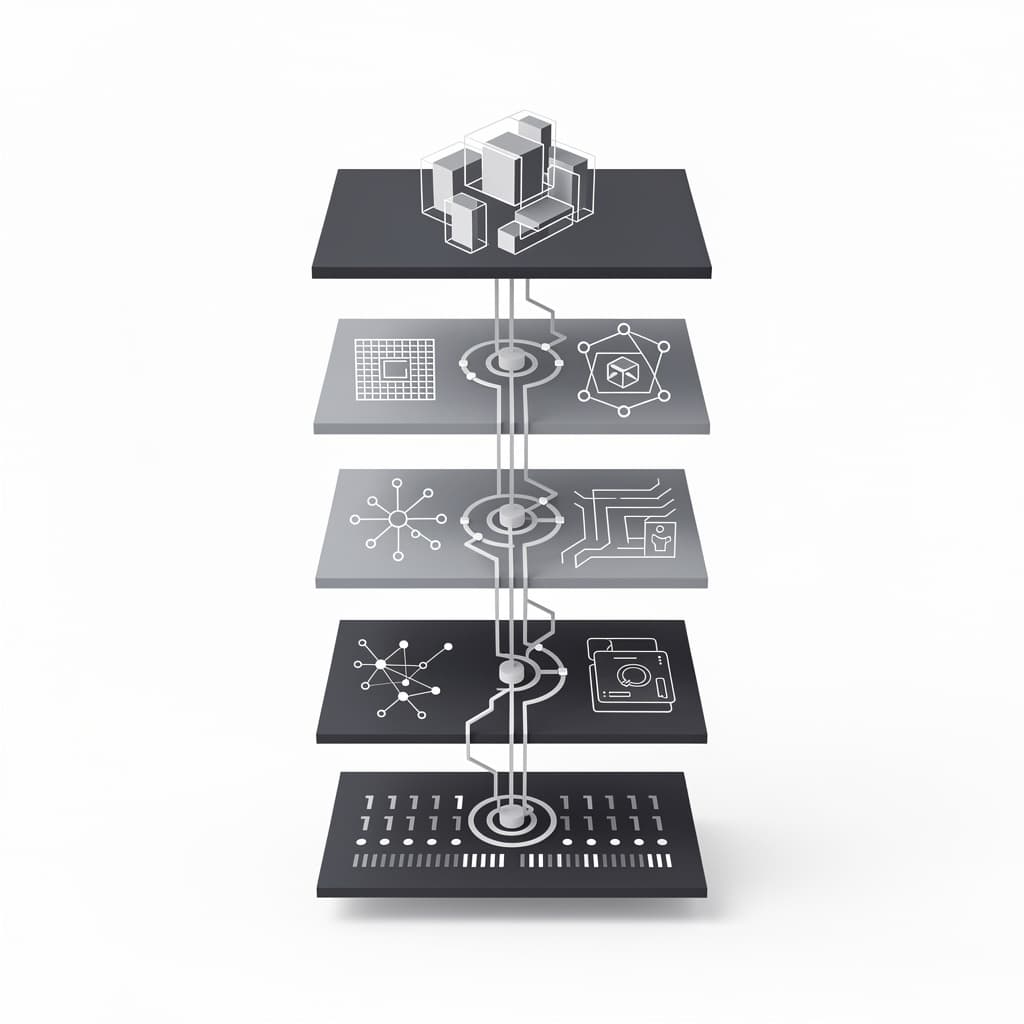
The Architectural Logic of the OSI Model
The Open Systems Interconnection (OSI) model serves as the primary conceptual blueprint for understanding how diverse computing systems communicate across a network environment. Developed by the...
Theoretical Foundations of the OSI Model
The historical context of the OSI model is rooted in the early chaos of the computing industry, where every major manufacturer developed its own proprietary networking protocols. During the 1970s, systems from IBM, Digital Equipment Corporation (DEC), and Honeywell were largely incompatible, creating "islands of automation" that could not exchange data without complex, expensive gateways. The ISO recognized that for the burgeoning field of telecommunications to flourish, a universal standard was required to define how data should be handled from the physical wire to the user application. This led to the creation of the Open Systems Interconnection subcommittee, which sought to establish a model that would promote competition and innovation by allowing different vendors to specialize in different layers of the stack. The primary logic behind the OSI model is the principle of modularity and abstraction, which isolates specific functions within dedicated layers. This modular communication ensures that a change in one layer—such as upgrading from copper wire to fiber optics—does not require a total redesign of the software applications running at the top of the stack. Each layer communicates with its "peer" on the receiving device through a process involving headers and trailers, ensuring that the integrity and context of the data are maintained throughout the journey. This vertical hierarchy allows engineers to focus on specific problems, such as signal interference at the physical level, without being distracted by the complexities of session management or user interfaces. Interoperability is the ultimate goal of the OSI framework, providing a common language for the entire technology industry. When we speak of a "Layer 3 switch" or a "Layer 7 firewall," we are using the OSI model to precisely define the scope of a device’s capabilities. This standardization has allowed for the explosion of the modern internet, as it provided the theoretical foundation upon which the TCP/IP protocol suite was refined and implemented. While the OSI model itself is often viewed as a theoretical construct, its influence is visible in every modern networking protocol, acting as the definitive map for the flow of digital information across the globe.Physical Layer versus Data Link Layer Mechanics
The Physical Layer (Layer 1) represents the most tangible aspect of the networking stack, focusing on the actual hardware used for data transmission. This layer is responsible for the transmission and reception of unstructured raw bitstreams over a physical medium, whether that medium is electrical voltage on a copper wire, pulses of light in a fiber-optic cable, or radio waves in the atmosphere. It defines technical specifications such as pinouts, voltages, cable types, and radio frequencies, ensuring that the 1s and 0s generated by a computer are correctly translated into signals that can travel through space or material. Without the stringent definitions of the Physical Layer, the electrical "noise" on a wire would be indistinguishable from actual data. In contrast, the Data Link Layer (Layer 2) provides the first level of logical structure to the raw bits coming from the Physical Layer. Its primary function is to transform a "raw" transmission facility into a line that appears free of undetected transmission errors to the Network Layer. It achieves this by organizing bits into discrete blocks called frames, which include a header containing the physical addresses of the sender and receiver. This layer is where MAC (Media Access Control) addresses reside, acting as the unique identifiers for network interface cards. By implementing error-checking mechanisms like the Cyclic Redundancy Check (CRC), the Data Link Layer ensures that the data arriving at a destination is identical to the data that was sent. The distinction between these two layers is vital for understanding local area network (LAN) operations. While the Physical Layer deals with the "how" of transmission (e.g., Cat6 cable vs. 802.11ax Wi-Fi), the Data Link Layer deals with the "who" and "when" of the local conversation. It manages media access control, determining which device has the right to transmit on a shared medium to prevent collisions. For example, in an Ethernet environment, the Data Link Layer uses protocols to sense when the wire is clear, while the Physical Layer simply handles the voltage fluctuations. Together, these two layers form the bedrock of local connectivity, moving data from one physical port to another within the same network segment.Routing Logic and Network Layer Protocols
The Network Layer (Layer 3) is where the concept of a "network of networks" truly begins, as it is responsible for moving data between different geographical or logical locations. While the Data Link Layer can only move data between devices on the same local segment, the Network Layer uses logical addressing—most commonly Internet Protocol (IP) addresses—to identify devices across the global internetwork. This layer acts as the post office of the digital world, determining the best path for a piece of data to take through a complex web of interconnected routers. By decoupling the identity of a device from its physical hardware address, the Network Layer allows for the massive scalability that defines modern telecommunications. Path determination, often referred to as routing, is the most critical function of the Network Layer. Routers maintain complex tables and use sophisticated algorithms to calculate the most efficient route for packets based on factors like hop count, bandwidth, and current congestion levels. When a packet arrives at a router, the Network Layer inspects the destination IP address and consults its routing table to decide which interface the packet should be forwarded through. This process happens millions of times per second across the internet, allowing a packet sent from a server in Tokyo to find its way to a laptop in London through a series of intermediate hops, each chosen dynamically based on real-time conditions. Another essential function of the Network Layer is fragmentation and reassembly. Since different network technologies have different limits on the maximum size of a data unit—known as the Maximum Transmission Unit (MTU)—a packet that is too large for a particular network segment must be broken into smaller pieces. The Network Layer handles this splitting process at the source or at an intermediate router and ensures that the receiving device has the information necessary to put the pieces back together in the correct order. This layer essentially masks the underlying complexities and limitations of diverse physical media, presenting a seamless, end-to-end logical connection to the layers above it.Reliability Systems within the Transport Layer
The Transport Layer (Layer 4) serves as the critical bridge between the hardware-oriented lower layers and the software-oriented upper layers. Its primary responsibility is to provide transparent, reliable, and cost-effective data transfer between the source and the destination, regardless of the physical networks being used. This is the first layer where the concept of end-to-end communication is fully realized, as it manages the conversation between the specific applications on two different devices. By using sequence numbers and acknowledgments, the Transport Layer can detect if a piece of data was lost during transit and request a retransmission, ensuring that the final data stream is complete and error-free. Two major protocols dominate this layer: the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP). TCP is a connection-oriented protocol that prioritizes reliability and order, making it ideal for web browsing, email, and file transfers where every bit must be accurate. It implements flow control using a technique called "sliding windows," which allows the receiver to tell the sender to slow down if it is being overwhelmed with data. Conversely, UDP is a connectionless protocol that prioritizes speed and efficiency over reliability. It is used for real-time applications like voice-over-IP (VoIP) and online gaming, where a dropped packet is less damaging than the delay caused by waiting for a retransmission. Port multiplexing is another vital function of the Transport Layer, allowing a single IP address to support hundreds of simultaneous connections. Each application on a computer is assigned a port number (e.g., port 80 for HTTP, port 443 for HTTPS), which the Transport Layer uses to direct incoming data to the correct software process. Without port numbers, a computer would have no way of knowing whether an incoming packet belonged to a web browser, an email client, or a background system update. By managing these individual "conversations," the Transport Layer ensures that data is not only delivered to the right house (the IP address) but also to the right person inside that house (the application port).Managing Connections via the Session Layer
The Session Layer (Layer 5) is perhaps the least understood layer of the OSI model, yet it performs the essential task of managing the "dialogue" between two computers. It establishes, manages, and terminates connections between local and remote applications, acting as the moderator of a conversation. While the Transport Layer handles the actual movement of data, the Session Layer handles the logistics of the interaction itself, such as deciding who speaks first and for how long. This is particularly important in environments where multiple applications are competing for network resources or where a single transaction involves several distinct steps that must be synchronized. One of the most critical services provided by the Session Layer is checkpointing and recovery. In the event of a network failure during a large file transfer, the Session Layer can use "synchronization points" to resume the transfer from the last known good state rather than starting from the very beginning. For example, if you are downloading a 2GB file and the connection drops at 1.5GB, a well-implemented session-layer service allows the transfer to pick up exactly where it left off. This layer also manages token management, preventing two parties from attempting the same critical operation at the same time, which is essential for maintaining data consistency in distributed databases. Dialog management at Layer 5 determines the mode of communication: simplex (one-way), half-duplex (two-way but one at a time), or full-duplex (simultaneous two-way). By coordinating these modes, the Session Layer ensures that the applications on both ends remain in sync regarding the state of their interaction. Although many modern applications implement these functions directly within the application itself, the Session Layer remains a vital conceptual part of the OSI model because it defines the necessary logic for session persistence. In contemporary web architecture, "session cookies" and "session IDs" are the practical manifestations of these Layer 5 concepts, ensuring that a user remains "logged in" as they navigate between different pages of a website.Presentation and Application Layer Functions
The Presentation Layer (Layer 6) acts as the "translator" for the network, ensuring that data sent from the application layer of one system can be read by the application layer of another. Since different computer architectures may use different methods for representing data—such as ASCII versus EBCDIC for text, or different ways of ordering bytes (endianness)—the Presentation Layer standardizes the data format before it is transmitted. This layer is also the primary home for data encryption and decryption, such as the processes involved in Secure Sockets Layer (SSL) or Transport Layer Security (TLS). By handling these complex transformations here, the application itself doesn't need to worry about the underlying format of the data. Beyond translation and security, the Presentation Layer also manages data compression, which reduces the number of bits that need to be transmitted over the network. This is especially important for multimedia applications where large files like images, videos, or high-fidelity audio would otherwise consume excessive bandwidth. By compressing the data at the source and decompressing it at the destination, the Presentation Layer improves the efficiency and perceived speed of the network. Effectively, this layer ensures that the information is presented in a contextually appropriate and optimized manner, bridging the gap between raw data and human-readable information. The Application Layer (Layer 7) is the highest level of the OSI model and the one closest to the end-user. It is important to clarify that this layer is not the software application itself (like Chrome or Outlook), but rather the network service protocols that those applications use to communicate. When you type a URL into a browser, the browser interacts with the Application Layer via the Hypertext Transfer Protocol (HTTP). Similarly, when you send an email, your mail client uses the Simple Mail Transfer Protocol (SMTP). This layer provides the interface points that allow software to access network resources, offering services such as file transfers, directory services, and electronic messaging.Comparing the TCP/IP versus OSI Model
While the OSI model is the gold standard for networking education, the TCP/IP model is the practical reality of the modern internet. Developed by the Department of Defense (DoD) in the 1970s, the TCP/IP model preceded the OSI model and was designed with a more pragmatic, "it just works" philosophy. The most notable difference lies in the number of layers: TCP/IP typically uses four layers (Network Access, Internet, Transport, and Application) compared to OSI's seven. In the TCP/IP framework, the Session and Presentation layers are absorbed into the Application layer, as developers found it more efficient to handle encryption and session management directly within the software rather than as separate network-stack functions. The structural evolution of these models reflects a shift from theoretical perfection to industry efficiency. The OSI model is often described as a prescriptive model, defining how a network should be built, while TCP/IP is a descriptive model, defining how the internet actually works. In the OSI model, the boundaries between layers are strictly defined, whereas in TCP/IP, the protocols are often loosely coupled. For instance, the TCP/IP "Internet Layer" corresponds almost exactly to the OSI "Network Layer," but the TCP/IP "Network Access Layer" combines the functions of both the OSI Physical and Data Link layers."The OSI model is a beautiful piece of theoretical architecture that was unfortunately late to the party; the TCP/IP model was the messy, functional guest that arrived early and never left."Today, the industry uses a hybrid approach. Engineers often use the OSI layer numbers to describe networking hardware (e.g., calling a router a "Layer 3 device") while actually implementing the TCP/IP protocol suite. This illustrates the enduring value of the OSI model as a teaching tool and a diagnostic framework. Even though we do not literally use seven distinct layers of software in a modern operating system, the logical separation provided by the OSI model remains the most effective way to visualize the complex journey of data as it moves from a user's fingertips to a destination halfway around the world.
Memory Techniques and the OSI Model Mnemonic
Memorizing the seven layers in order—Physical, Data Link, Network, Transport, Session, Presentation, Application—is a rite of passage for students of computer science. To aid this process, educators have developed several popular OSI model mnemonics that help cement the order in our minds. For those moving from the bottom (Layer 1) to the top (Layer 7), the most common phrase is: "Please Do Not Throw Sausage Pizza Away." Conversely, if you prefer to remember them from the top (Layer 7) down to the bottom (Layer 1), the standard mnemonic is: "All People Seem To Need Data Processing." These simple sentences provide a mental hook for the first letter of each layer, turning an abstract list into a memorable sequence. Beyond simple memorization, it is crucial to visualize the data encapsulation cycle to understand how the layers actually interact. As data moves down the stack from the Application layer to the Physical layer, each layer adds its own specific "header" (and sometimes a trailer) to the data. This process is called encapsulation. You can imagine it like a set of nesting Russian dolls or a letter being placed in multiple envelopes. The Application layer creates the data, the Transport layer adds a header to create a segment, the Network layer adds an IP header to create a packet, and the Data Link layer adds a MAC header to create a frame. Finally, the Physical layer converts that frame into bits for transmission. Upon reaching the destination, the process is reversed in what is known as decapsulation. Each layer on the receiving device strips off the header intended for its peer on the sending device, inspects the information for errors or routing instructions, and passes the remaining data up to the next layer. This cyclical process ensures that the Application layer on the receiving end sees the exact same "data" that was sent by the source, completely unaware of the complex transformations and headers that were applied during the journey. This elegant "hand-off" mechanism is what allows the OSI model to function as a unified, coherent system for global communication, proving that even in the high-speed world of modern fiber optics, the logic of the 1980s still holds firm.References
- Zimmermann, H., "OSI Reference Model—The ISO Model of Architecture for Open Systems Interconnection", IEEE Transactions on Communications, 1980.
- Tanenbaum, A. S., & Wetherall, D. J., "Computer Networks", Pearson Education, 2011.
- Day, J. D., & Zimmermann, H., "The OSI Reference Model", Proceedings of the IEEE, 1983.
- International Organization for Standardization, "ISO/IEC 7498-1:1994 Information technology — Open Systems Interconnection — Basic Reference Model", ISO Standard, 1994.
Recommended Readings
- Computer Networking: A Top-Down Approach by James Kurose and Keith Ross — Provides a modern, application-first perspective on how the layers interact in real-world scenarios.
- TCP/IP Illustrated, Vol. 1: The Protocols by W. Richard Stevens — A deep-dive technical classic that explains how the theoretical layers are implemented in actual code.
- Interconnections: Bridges, Routers, Switches, and Internetworking Protocols by Radia Perlman — An authoritative look at the Layer 2 and Layer 3 logic that makes the internet possible.
- The Essential Guide to Networking by James Keogh — A highly accessible introduction to networking fundamentals for those new to the OSI framework.